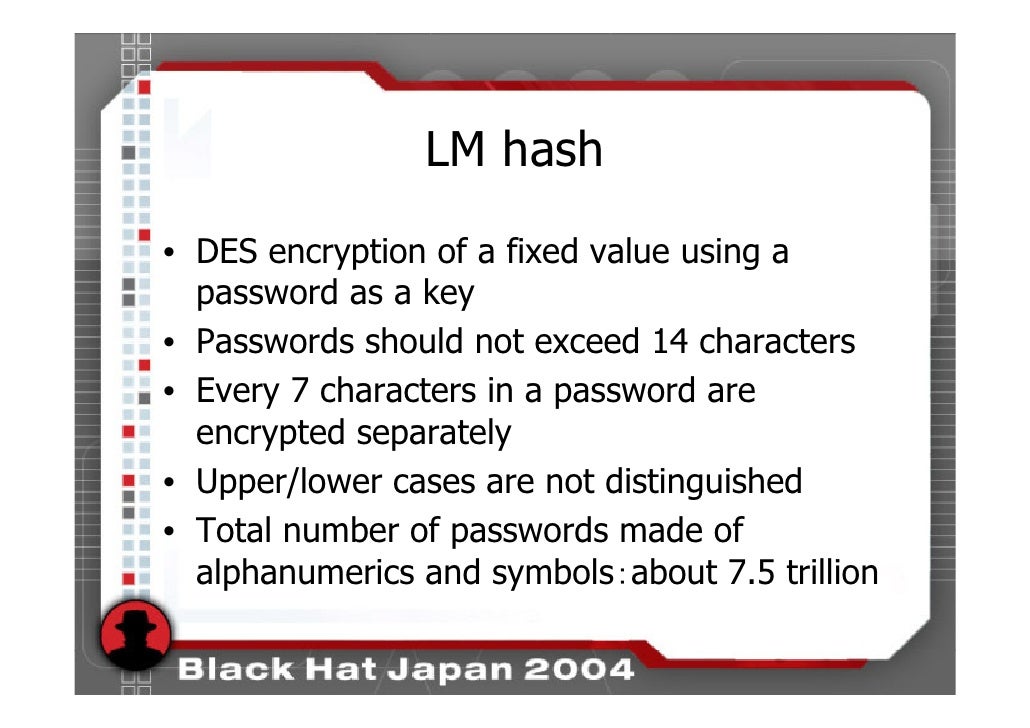
Analytics cookies. We use analytics cookies to understand how you use our websites so we can make them better, e.g. They're used to gather information about the pages you visit and how many clicks you need to accomplish a task. The LM hash is the old style hash used in Microsoft OS before NT 3.1. Then, NTLM was introduced and supports password length greater than 14. On Vista, 7, 8 and 10 LM hash is supported for backward compatibility but is disabled by default. The goal is too extract LM and/or NTLM hashes from the system, either live or dead.
Practice ntds.dit File Part 3: Password Cracking With hashcat – Wordlist
Now we will use hashcat and the rockyou wordlist to crack the passwords for the hashes we extracted in part 2.
With this command we let hashcat work on the LM hashes we extracted:
Option -a 0 instructs hashcat to perform a straight attack.
Option -m 3000 informs hashcat that we provide LM hashes.
Option –username informs hashcat that the hash file lm.ocl.out includes usernames.
Argument lm.ocl.out is the hash file.
Argument rockyou.txt is the wordlist.
I also use option –potfile-path to instruct hashcat to use a specific pot file (a file containing the cracked hashes with corresponding passwords).
Here is the output:
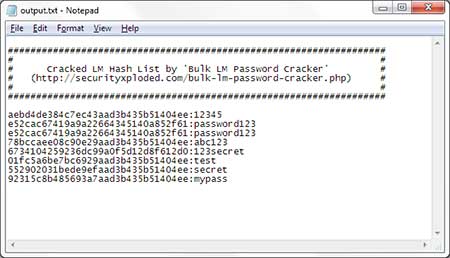
To display the cracked passwords, we use option –show:
Option –show instructs hashcat to display the cracked passwords.
Option -m 3000 informs hashcat that we provide LM hashes. This is necessary for –show.
Option –username informs hashcat that the hash file lm.ocl.out includes usernames.
Option –outfile-format 2 instructs hashcat to output the password without the hash.

Argument lm.ocl.out is the hash file.
I also use option –potfile-path to instruct hashcat to use a specific pot file (a file containing the cracked hashes with corresponding passwords).
Here is the output:
As you can see we cracked most of the passwords for users 1 through 20, except when the password is longer than 14 characters. Also remark that all passwords are uppercase.
With this command we let hashcat work on the NTLM hashes we extracted:
The options and arguments are almost the same as for the LM command, except:
Option -m 1000 informs hashcat that we provide NTLM hashes.
Argument nt.ocl.out is the hash file.
Here is the output:
Remark that this time we cracked all passwords for users 1 through 20 (also the ones longer than 14 characters), and with the proper case.
Sponsored adsHash Decoder
Hash Calculator
Tool to decrypt / encrypt with hash functions (MD5, SHA1, SHA256, bcrypt, etc.) automatically. The hashing of a given data creates a fingerprint that makes it possible to identify the initial data with a high probability (very useful in computer science and cryptography).
Answers to Questions
How to calculate/encode a hash?
The hash functions use computer data (in binary format) and apply nonlinear and non-reversible functions with a strong avalanche effect (the result is very different even if the input data is very similar). The fingerprint is usually returned as hexadecimal characters.
Example:dCode has for hashMD5e9837d47b610ee29399831f917791a44
Example:dCode has for hashSHA115fc6eed5ed024bfb86c4130f998dde437f528ee
Example:dCode has for hashSHA256254cd63ece8595b5c503783d596803f1552e0733d02fe4080b217eadb17711dd
See the dCode pages for each hash function to know how it works in detail: MD5, SHA1, SHA256, etc.
How to decrypt a hash?
The principle of hashing is not to be reversible, there is no decryption algorithm, that's why it is used for storing passwords: it is stored encrypted and not unhashable.
Example:123+456=579, from 579 how to find 123 and 456? This is not possible except by trying all possible combinations.
The hash functions apply millions of non-reversible operations so that the input data can not be retrieved.
Crack Lm Hash Nt Hash Decrypt Machine
Hash functions are created to not be decrypable, their algorithms are public. The only way to decrypt a hash is to know the input data.
What are rainbow tables?
Theoretically, a brute-force mode is possible by testing all the binary strings, but a short message of 6 bytes already represents 281,000 billion combinations. Even with fast processors capable of performing millions of hash calculations per second, several days, months or years of calculations are therefore necessary to try all the possibilities in order to find a single hash.
However, users generally always use the same passwords and some characters more than others, so it is possible to store the most likely binary strings and their respective hashes in a very large dictionary. These dictionaries are called rainbow tables. These tables make it possible to test all the words of a given dictionary to check if their fingerprint corresponds to a given one.
Example: dCode uses its word and password databases with millions of pre-calculated hashes.
If the word is not in the dictionary, then there will be no result.
Crack Lm Hashes
How to recognize a hash?
A hash can take many forms, but the most common are hexadecimal strings: 32 characters 0123456789abcdef for the MD5, 40 for the SHA-1, 64 for the SHA-256, etc.
The encoding system based on bcrypt uses the symbol $ followed by a number indicating the algorithm used and its possible parameters.
What is a salt (for a hash)?
The rainbow tables (gigantic databases of hash and password matches) are growing day by day and accumulating passwords stolen from various sites, and taking advantage of the computational performance of super calculators, allow today to decipher short passwords in minutes / hours.
In order to counter this technique, it is recommended to add salt (some characters in prefix or suffix) to the password/message. In this way, the precalculated tables must again be calculated to account for the salt that systematically modifies all the fingerprints, the salting step. Passwords are salted.
Example:MD5(dCode) = e9837d47b610ee29399831f917791a44 and MD5 (dCodeSUFFIX) = 523e9a80afc1d2766c3e3d8f132d4991

What is a cost (for a hash)?
Cost is the measure of the resources needed to calculate a hash. In order to complicate the task of creating the rainbow tables, it is possible to complicate some hashes so that the calculations take several milliseconds or seconds, which makes the duration necessary for the attacks too great to be applicable.
What is bcrypt?
bcrypt is a library of cryptographic functions that applies recursion rules to hash functions. Natively, the notions of salt and cost are applicable.

Source code
dCode retains ownership of the online 'Hash Function' tool source code. Except explicit open source licence (indicated CC / Creative Commons / free), any algorithm, applet or snippet (converter, solver, encryption / decryption, encoding / decoding, ciphering / deciphering, translator), or any function (convert, solve, decrypt / encrypt, decipher / cipher, decode / encode, translate) written in any informatic language (PHP, Java, C#, Python, Javascript, Matlab, etc.) no data, script or API access will be for free, same for Hash Function download for offline use on PC, tablet, iPhone or Android !
Need Help ?
Please, check our community Discord for help requests!